In this article we are going to show how we can crack /etc/shadow file using John the Ripper. It is common in CTF like events to somehow get access to the shadow file or part of it and having to crack it so you can get the password of a user.
The process involves two basic steps, the first is called unshadowing while the second is the cracking itself. Unshadowing is a process where we combine the /etc/passwd file along with the /etc/shadow in order for John to be able to understand what we are feeding to it. Unshadow is a tool that handles this task and it is part of the John package. In order to unshadow the shadow file we need to also have the equivalent line from the passwd for the user of our interest. An example is the following:
# /etc/passwd line
root:x:0:0:root:/root:/bin/bash
# /etc/shadow line
root:$6$riekpK4m$uBdaAyK0j9WfMzvcSKYVfyEHGtBfnfpiVbYbzbVmfbneEbo0wSijW1GQussvJSk8X1M56kzgGj8f7DFN1h4dy1:18226:0:99999:7:::
In order to unshadow to the two files we need to execute
unshadow passwd.txt shadow.txt > unshadowed.txt
Which will store in the unshadowed.txt file the following
root:$6$riekpK4m$uBdaAyK0j9WfMzvcSKYVfyEHGtBfnfpiVbYbzbVmfbneEbo0wSijW1GQussvJSk8X1M56kzgGj8f7DFN1h4dy1:0:0:root:/root:/bin/bashNext and final step is to actually start the cracking with John. It is up to you which cracking method you will chose, though a bruteforcing using a wordlist is usually enough for CTFs. An example attack using a wordlist would be launched like below
john --wordlist=/usr/share/wordlists/rockyou.txt unshadowed.txtThe result would be similar to the following picture
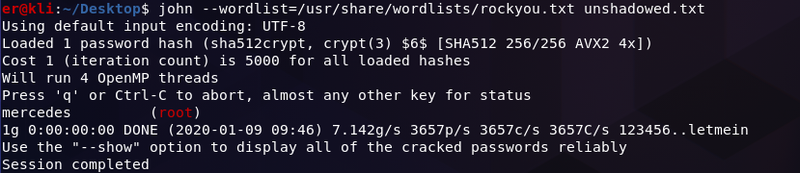
Where as we see John managed to crack the password of the user root as it was included in the wordlist used.
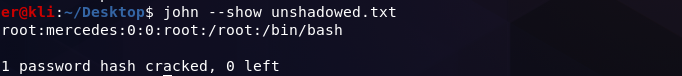
If you would like to print all the passwords John managed to crack you may run john --show unshadowed.txt and you will get something like:
Conclusion
In this article we showed how John the Ripper can be used to crack the hashed password of a user that can be found in the /etc/shadow file. The process is pretty simple and straightforward yet if you find yourself stuck somewhere please feel free to reach out to me.